Security testing is all about actively trying to break into a system to find its weak spots. Think of it like a "digital home inspection." Instead of a professional checking for a cracked foundation or faulty wiring, a security expert is looking for digital vulnerabilities—like an unlocked back door or a flimsy window latch—before a real burglar finds them.
A Digital Inspection for Your Smart Home

Let's say you just installed a new smart security camera. You bought it to watch over your home, but have you ever stopped to think about who might be watching the camera itself?
That simple question gets right to the heart of security testing. It's a deliberate, proactive process designed to find and patch security flaws before someone with bad intentions can take advantage of them.
In a modern smart home, every single connected device is a potential doorway for an intruder. Your thermostat, your voice assistant, your smart lock—they all represent a possible point of entry. Security testing is the practice of systematically poking and prodding these devices, their software, and the network they run on to hunt for those hidden risks.
Identifying Hidden Risks
The goal here is to stop assuming your digital defenses are strong and start actively challenging them. This isn't just about warding off stereotypical "hackers," either. It's about making sure the technology you lean on for comfort and safety doesn't accidentally become a source of risk. A good security test will zero in on common, easily overlooked problems.
- Default Credentials: Did you know many devices come out of the box with generic usernames and passwords like "admin"? These are often public knowledge. A test checks to see if they've been changed.
- Unsecured Networks: It confirms your Wi-Fi is properly encrypted and that your smart devices aren't just broadcasting their communications for anyone to hear.
- Outdated Software: Testers hunt for devices running old firmware. If a known vulnerability exists for that version, it's a major red flag.
- Exposed Services: Sometimes, a feature meant only for your local home network can be accidentally exposed to the entire internet, essentially leaving a door wide open.
At its core, security testing is about learning to think like an attacker. It’s a methodical process of probing for weaknesses and constantly asking, "If I wanted to get in, how would I do it?" Adopting this mindset is key to uncovering flaws that are completely invisible from a normal user's point of view.
Gaining Control and Visibility
So, what is security testing? It’s about building confidence in the technology you use every day. By finding and fixing vulnerabilities, you can be sure your smart home stays your private sanctuary.
A fantastic first step is simply getting a clear overview of every connected device you own. Centralized dashboards, like the amazing ones I create for my Home Assistant setup using Dashable, give you a single command center for your entire smart home. This kind of visibility makes it so much easier to track what's connected, check its status, and make sure every device is accounted for and locked down.
Why Security Testing Is No Longer Optional

Think about every smart device you bring into your home—from a simple lightbulb to a high-tech thermostat. Each one is another potential doorway for digital intruders. We’re well past the point of abstract fears; the risks of overlooking security are real, tangible, and growing by the day.
A single, poorly secured gadget can be the weak link that compromises your entire home network. This isn't about some Hollywood hacker in a dark room. It’s about preventing practical, disruptive problems that can turn your own smart home against you. Without proper testing, your network is an open invitation.
The Tangible Risks You Face
The threats aren’t just hypotheticals. They are real-world scenarios that pop up when security is treated as an afterthought.
- Unauthorized Access: Imagine an attacker gaining control of your security cameras, smart locks, or microphones. It’s a violation of your privacy in the most personal way possible.
- Personal Data Theft: Your home network is a goldmine of sensitive information. Weak security can expose everything from your browsing habits to financial details stored on connected computers.
- Device Hijacking: Your smart devices could be secretly commandeered and used in a "botnet" to attack websites and services, making you an unwilling accomplice in cybercrime.
The real problem is complexity. An insecure smart plug from a no-name brand might have a built-in backdoor. That tiny flaw could let an intruder slip right past your router's firewall, giving them free rein over every other device you own.
This deep interconnectedness is precisely why security testing is so critical. It’s the only way to be sure your technology is working for you, not against you. The scale of the problem is staggering; in a recent year, data breaches exposed nearly 6.85 billion records worldwide.
Building a Defensible Smart Home
Creating a truly safe and reliable smart home starts with a simple principle: understanding and controlling access. Knowing exactly what’s on your network and how it’s configured is the first, most fundamental step. For example, when you learn how to set up Home Assistant for remote access, you’re actively taking control of your smart home's digital perimeter.
This is why tools that offer a central command center are so valuable. A dashboard built with a platform like Dashable can give you an at-a-glance overview of your entire system. It makes spotting unusual activity, managing device settings, and ensuring your smart home remains your private sanctuary—not an open house for intruders—so much easier.
Exploring Different Security Testing Methods
When it comes to securing a system, there’s no one-size-fits-all solution. Think about building a smart home—you wouldn’t use a single tool for everything from plumbing to electrical work. In the same way, a strong security plan relies on a mix of different testing methods, each designed to uncover specific types of weaknesses. Getting to know these approaches helps lift the curtain on how experts keep our digital lives safe.
Let's stick with that home security analogy. You probably have a nightly routine where you walk around and check that all the doors and windows are locked. This is a lot like Vulnerability Scanning. It's an automated process that uses specialized tools to quickly check for known, common weak points, like out-of-date software or simple configuration errors. It’s an excellent first line of defense for catching the low-hanging fruit.
But a routine lock check won't tell you how a determined burglar might actually get inside. For that, you need to think like one.
Simulating a Real-World Attack
This is exactly what Penetration Testing, or "pen testing," is all about. If vulnerability scanning is checking the locks, pen testing is hiring a professional (an ethical hacker) to actively try to break into your house. They won’t just check the locks; they’ll jiggle the handles, look for a spare key under the mat, and even test the strength of the window frames to see what gives.
Their mission isn't to do any damage, of course. It's to find and exploit real-world flaws and then give you a detailed report on exactly how they broke in. This hands-on approach is vital for discovering complex or novel vulnerabilities that an automated scan would simply never catch. It gives you a true picture of how well your system holds up against a real attacker.
Another crucial aspect of testing is how much the tester knows about the system beforehand. This is often broken down into three main perspectives, as shown below.
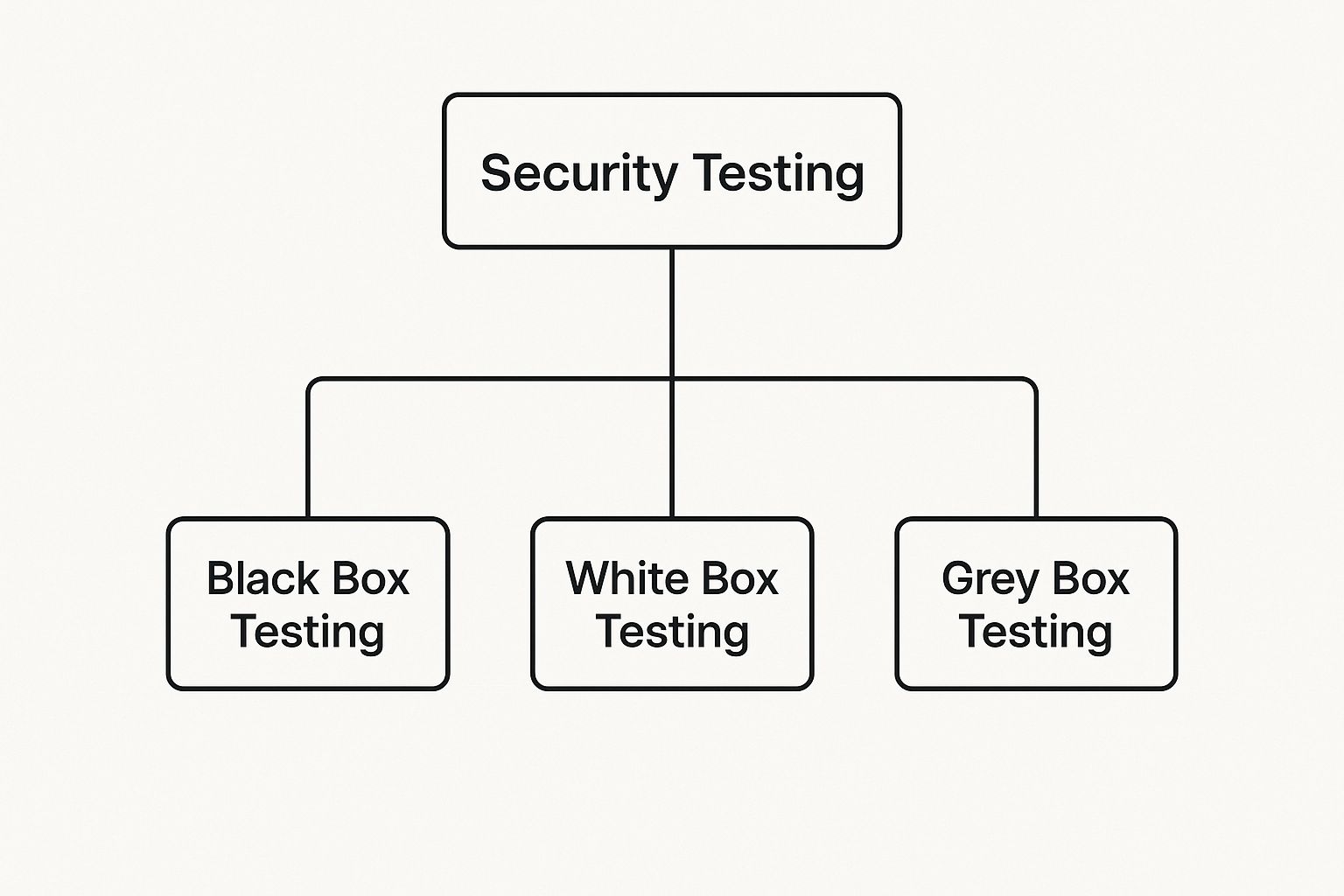
As you can see, testing can be done with zero knowledge (Black Box), complete internal access (White Box), or something in between (Grey Box), each simulating a different type of threat.
Comparing Common Security Testing Methods
To make these concepts even clearer, here’s a quick comparison of the most common methods using our smart home analogy. This table breaks down what each test does and how it relates to protecting your home.
| Testing Type | Main Purpose | Smart Home Analogy |
|---|---|---|
| Vulnerability Scanning | Automated check for known, common weaknesses | A nightly routine of walking around and checking that all doors and windows are locked. |
| Penetration Testing | Simulating a real attack to find exploitable flaws | Hiring an ethical "burglar" to actively try and break into your home to test its real-world defenses. |
| Static Testing (SAST) | Analyzing source code for flaws before running the app | Reviewing the blueprints of your house's security system before it's even installed. |
| Dynamic Testing (DAST) | Testing a running application from the outside | Arming your installed security system and then trying to trigger the alarms from the outside. |
Each of these methods provides a unique view of your security posture. Relying on just one would be like only locking the front door while leaving the back window wide open.
Looking Inside vs. Outside
Beyond the attacker's point of view, testing also varies based on whether we’re looking at the system from the inside out or the outside in. Two fundamental techniques provide this comprehensive coverage.
-
Static Application Security Testing (SAST): This is like having an expert examine your home’s security blueprints before construction even begins. SAST tools inspect an application's source code without ever running it, hunting for coding mistakes and structural flaws that could create vulnerabilities down the line.
-
Dynamic Application Security Testing (DAST): This approach tests the application while it’s actually running—much like you'd test your home alarm system after it's been installed and armed. DAST sends simulated attacks to the live application to see how it behaves, uncovering security holes that only surface during operation.
A truly robust security strategy weaves these methods together. For example, I use a dashboard from Dashable to monitor my live smart home devices (that’s your dynamic view), while the developers of those devices use SAST to make sure the code is solid before it ever gets to you. This layered approach is what creates a truly resilient defense.
How a Security Test Uncovers Vulnerabilities

It’s one thing to know what security testing is, but seeing how it actually works is where the lightbulb really goes on. A professional security test isn’t some chaotic, brute-force attack; it’s a highly structured process, almost like a detective methodically solving a complex case.
Each phase builds on the last, moving from wide-angle reconnaissance to pinpointing specific, fixable flaws. This systematic approach is the secret sauce. It’s what separates a professional audit from someone just randomly jiggling doorknobs on your network. Instead, the pros have a full blueprint and are checking every single potential entry point.
Let's walk through the four core phases of a typical security test to see how the magic happens.
The Four Phases of a Security Test
A solid test always follows a logical flow: plan, scan, attack, and report. This structure makes sure that vulnerabilities aren't just found but are also fully understood, prioritized, and ultimately, fixed.
-
Planning and Reconnaissance
This first step is all about gathering intel. Before any active testing begins, the security expert carefully maps out the entire "attack surface." Think of it like a burglar casing a house to learn its layout, find all the doors and windows, and observe the daily routines. In the digital world, this means identifying every server, application, and connected device to understand how they all talk to each other. -
Scanning
With the map complete, the next move is to scan for obvious weak spots. Using a suite of automated tools, testers sweep the system for known vulnerabilities. This is the low-hanging fruit. It might be a server with a port left wide open to the internet or a new piece of software still using its factory-default password (like "admin123").
This scanning phase is a massive time-saver. It quickly flags common, high-risk issues, which lets the expert focus their manual, hands-on testing time on uncovering the deeper, more complex vulnerabilities that automated tools almost always miss.
-
Exploitation (Gaining Access)
Here’s where the rubber meets the road. Once a potential vulnerability is found, the tester actively tries to exploit it. This isn't about causing damage; it's about proving the weakness is a real, tangible threat. For example, they might use that default password found during the scan to log into an admin panel, demonstrating that a real attacker could do the exact same thing. This step is crucial for validating the risk. -
Reporting and Remediation
Finally, the tester compiles everything into a detailed report. A good report doesn't just list a bunch of problems. It clearly explains the business risk of each vulnerability and provides actionable, step-by-step instructions on how to fix it. It might also offer guidance on strengthening your overall security, like showing you how to create a self-signed certificate to better secure internal communications.
This methodical process is precisely why the security testing market is exploding. Valued at USD 14.67 billion recently, it's projected to climb to an incredible USD 111.76 billion by 2033. Network security testing alone accounts for over 38% of that demand, a testament to how essential this work is in our connected world. You can dig into more of the numbers over at Grand View Research.
Practical Security Tips for Your Smart Home
Knowing the theory of security testing is great, but it's putting that knowledge into action that actually keeps your smart home safe. Let's get practical and walk through the concrete steps you can take right now. These aren’t just friendly suggestions; they're the foundational rules for building a smart home you can truly trust.
First up, and this is the big one: passwords. Using weak or recycled passwords is like leaving your front door unlocked with a welcome mat out for intruders. Every single smart device on your network needs its own strong, unique password.
This one step alone dramatically cuts down your risk. If a hacker manages to crack the password for one device, the damage is contained instead of spreading like wildfire through your entire network.
Building Your Smart Home Fortress
Once you've sorted out your passwords, it’s time to add more layers of defense. Think of it as reinforcing your digital walls and installing a top-notch alarm system.
- Enable Two-Factor Authentication (2FA): If a device or app offers 2FA, turn it on. No excuses. 2FA asks for a second piece of proof, usually a code from your phone, before granting access. This makes it incredibly difficult for someone to get in, even if they manage to steal your password.
- Keep Firmware Updated: Manufacturers constantly release updates to fix security holes they've found. The best approach is to set your devices to auto-update. If that’s not an option, get into a routine of checking for updates yourself at least once a month.
- Use Secure SSH Keys: If you're running a more advanced setup, like managing a Home Assistant server from afar, SSH keys are a world away from passwords in terms of security. For anyone running a Linux-based system, you can learn more about generating Linux SSH keys in our detailed guide.
Visibility is the cornerstone of control. You cannot secure what you cannot see. Knowing exactly what is connected to your network at all times is essential for identifying unauthorized devices or spotting unusual behavior before it becomes a major problem.
Having a central dashboard is the perfect way to get that bird's-eye view.
Gaining Command and Control
Trying to manage dozens of different devices, each with its own app and security settings, can quickly become a nightmare. It’s this complexity that often causes people to give up on security altogether. The trick is to find a single point of control.
A powerful tool like Dashable can act as a command center for your entire smart home. By pulling all your connected devices into one dashboard, you get a simple, at-a-glance overview of your whole network. This makes it so much easier to monitor what's happening, check that every device is accounted for, and confirm your security settings are all in place. It turns a chaotic web of gadgets into one manageable system.
This push for better security isn't just happening in our homes; it's a global focus. The security testing market is growing fast all over the world, particularly in the Asia-Pacific (APAC) region, which was valued at around USD 3.75 billion recently. You can discover more insights about this growing market to see how different regions are tackling this challenge.
Answering Your Top Smart Home Security Questions
Even when you get the basics of security testing, a few practical questions always come up. It's totally normal. Trying to secure a bunch of connected gadgets can feel a bit overwhelming, so let's clear up some of the most common sticking points.
Getting these questions answered will help you move forward and feel more confident that you're actually making your home safer, not just adding more complexity.
Is Security Testing Really Necessary for Just a Few Smart Devices?
Yes, 100%. People often think, "My little network is too small to be a target," but that's exactly the kind of thinking attackers rely on. They often go after smaller, less-defended systems because they're seen as easy wins.
Think of it this way: a single, forgotten smart plug with a factory-default password can be the unlocked window an intruder uses to get into your entire home network. Once they're in, they can potentially see personal files on your laptop or sniff out financial data. You wouldn't leave a small back window unlocked just because it's not the front door, right? The same logic applies here.
How Is Security Testing Different From Antivirus Software?
This is a fantastic question because it gets right to the core of proactive versus reactive security. They’re both crucial, but they play completely different roles.
Antivirus software is reactive. It's designed to spot and clean up known viruses and malware that have already found a way onto your computer. It’s like a security camera that records a break-in as it's happening.
Security testing is proactive. It’s the process of you actively checking all the locks, windows, and alarm sensors before anyone even tries to get in.
For a truly secure setup, you really need both. One is your defense against known threats that are actively trying to attack you, while the other is your quality control, making sure those defenses are actually strong enough to work.
How Often Should I Check My Smart Home Security?
The best approach is to build a simple, repeatable habit. A good starting point is to check for firmware updates on your devices every quarter and run a quick network scan once a month. This just helps you spot any new or unrecognized devices that might have joined your Wi-Fi.
Beyond that, plan on doing a more thorough review of your passwords and security settings twice a year. You should also do a quick check-up any time you add a new device to your network. This is where a centralized dashboard makes a huge difference. As a Home Assistant enthusiast, I can tell you that using a tool like Dashable to create a central dashboard pulls everything into one spot, so these regular check-ins go from being a chore to a quick, easy task.
Can I Do This Myself, or Do I Need to Hire an Expert?
The good news is that for most smart home owners, you can absolutely handle the most important security tasks on your own. The fundamentals have the biggest impact and don't require a cybersecurity degree.
- You've got this: Using strong, unique passwords for every single device, turning on two-factor authentication (2FA) whenever you see the option, and simply keeping your firmware updated are all things you can—and should—do yourself.
- When to call an expert: If you have an incredibly complex network, maybe one that's tied to a home business or stores very sensitive data, then a professional "penetration test" might be worth it. They can find deep-seated issues that basic checks and automated tools would likely miss.
For the average enthusiast, though, just mastering the basics will put you miles ahead of the curve.
Ready to gain complete visibility and control over your smart home? Dashable lets you build stunning, easy-to-use dashboards for your Home Assistant setup, making it simpler than ever to monitor and secure all your connected devices from one place. Learn more and start building your command center at https://dashable.app.